Congratulations! You now have Mutillidae installed, on either Windows or Linux. You should be able to access it from any host on the intranet with the same subnet mask. I invite you to start getting familiar with the site by clicking around on the top and left menus.
Using Mutillidae
User registration
Let me give you a quick overview of how to start using Mutillidae.
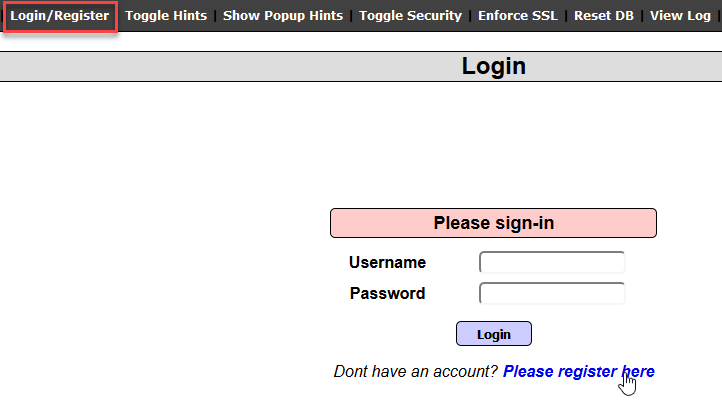
First, let's register an account to use in our pen test, later in this book. On the top menu, click on the Login/Register button, and you will be redirected to the login page:
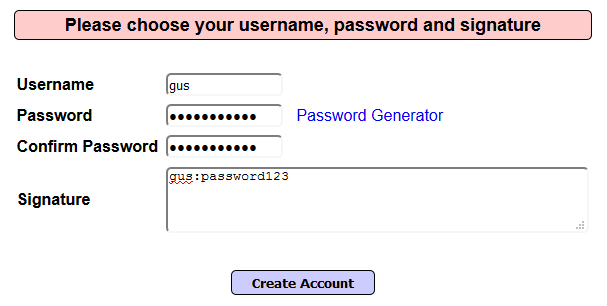
You guessed it! On this page, click on Please register here to go to the registration page. Let's register a user, gus, and a super secret password, password123:
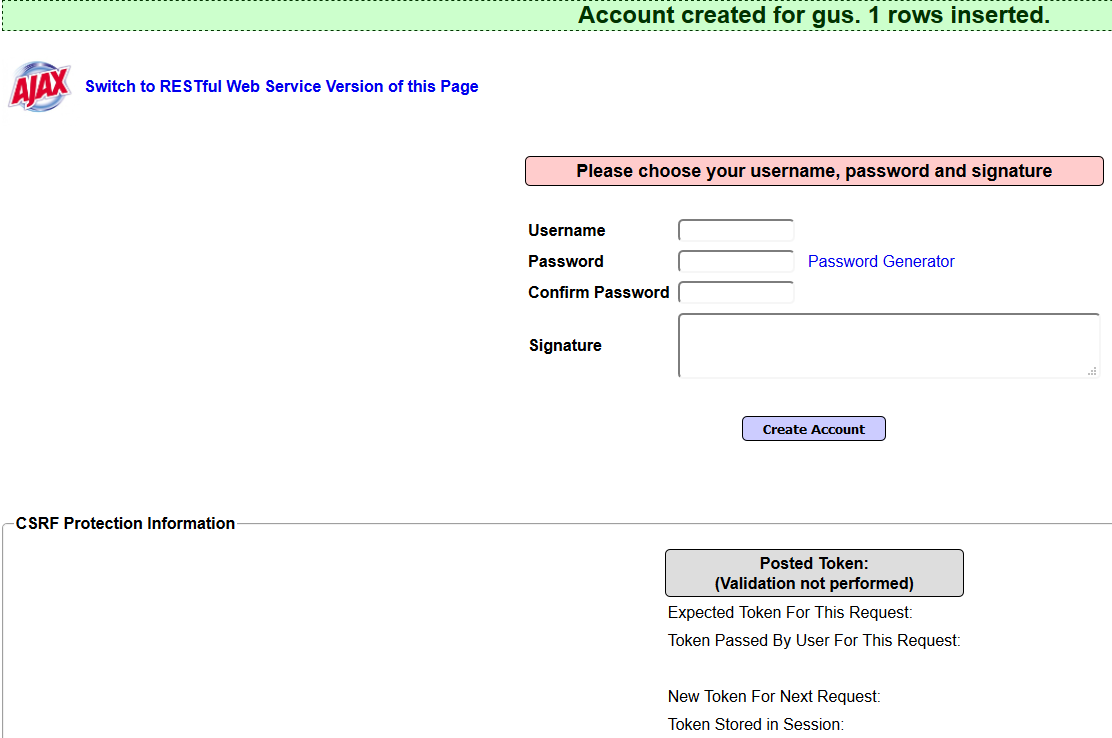
Finally, click on the Create Account button to create the account:
Showing hints and setting security levels
This application is meant for web application professionals who want to practice web application type vulnerabilities. (For example, SQL Injection, Cross-Site Scripting, and so on. Don't worry; you will learn about them later in this book.) While practicing, Mutillidae offers you the option to display hints, in case you are blocked and you can't find the vulnerability that you are trying to solve.
First, on the top menu, click the Toggle Hints button to enable/disable hints. Next, click on Show Popup Hints to enable the pop-up hints, and you will notice that the text changes to Hide Popup Hints, in case you change your mind and want to disable it again:

Also, you can change the complexity levels for hacking this application. By default, the security is set to 0 (completely vulnerable); click on the Toggle Security button, and the level will change to 1 (client side active). Click one more time, and the level 5 will be active (server side). If you want to go back to level 0, click on Toggle Security while you're in level 5, and it should go back to 1. I'm going to leave it on level 1 for the rest of this book.
Application reset
Things can go wrong, and the application can stop working. If this happens to Mutillidae, it means that your application is sick and needs some medication. No, I'm kidding! All you need to do is reset it. Resetting Mutillidae is simple; just click on the Reset DB button on the top menu bar, and your application will become brand new again.
OWASP Top 10
The Open Web Application Security Project (OWASP) is a community dedicated to helping people and organizations with application security topics. If you'll be working as an AppSec expert, then OWASP should be your bible; they have plenty of help sections that will make your life much easier. Just follow their guidelines and tutorials at http://www.owasp.org.
The OWASP community defined the Top 10 vulnerabilities related to web applications. As for Mutillidae, it dedicated a menu to these vulnerabilities. On the left menu, you will see the OWASP items organized by year (the latest is the OWASP Top 10 for 2017; see the following screenshot). OWASP always keeps this list updated with the latest web vulnerabilities:

I have dedicated a whole chapter to these vulnerabilities, later in this book. For the time being, try to get familiar with the menu items.