The following demonstration will be a more detailed Nmap lab to reinforce what you have learned earlier in the chapter. This lab uses Kali Linux running in VMware:
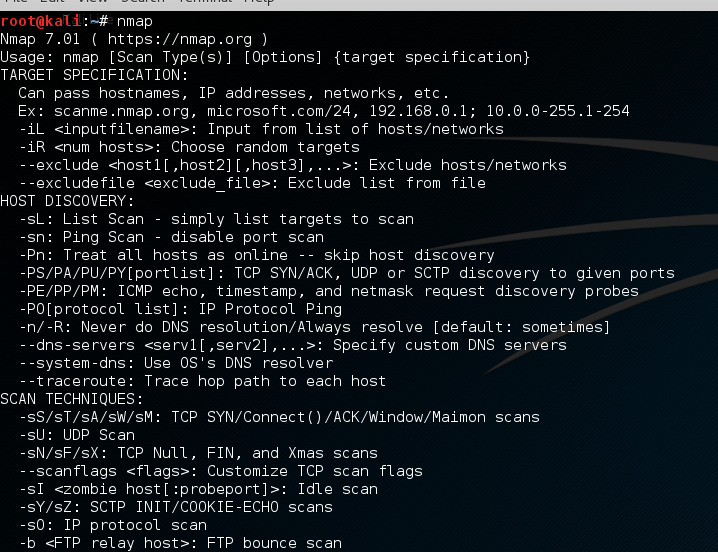
- Open Nmap in Kali.
- Open a terminal in Kali and type nmap.
When you do so, Nmap will display its help screen, as shown in the following screenshot:
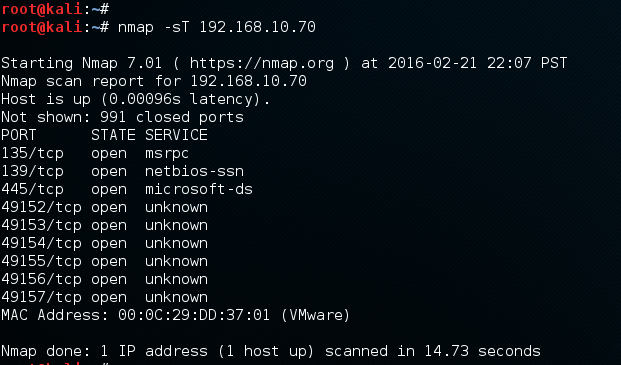
- Let's try to use the -sS and -sT scans.
Using Nmap's basic syntax, type in the following:
nmap <scantype> IP address
We get results like those shown in the following screenshot, showing all of the TCP ports that are open on our target machine and the default service for each port:
- Next, we can scan for a specific port or port range.
Nmap uses the -p switch to designate a port or port range. So, if we were only looking for ports 100-200, we could use the following:
kali > nmap 192.168.10.70 -p100-200
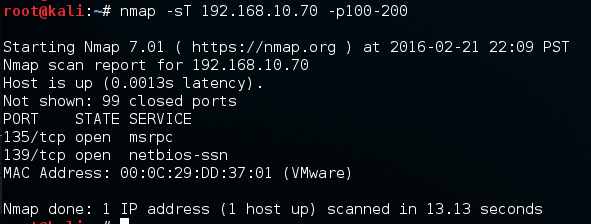
As you can see, this command scans and reveals...

























































