Understanding mobile forensics
Apple devices are popular all over the world due to the user experience they provide, their magnificent design, and their revolutionary features, so it shouldn't come as a surprise that in 2016, Apple announced that over one billion iPhones had been sold. Over the past 5 years, mobile device usage has grown particularly fast, with data from 2021 indicating that there were one billion active iOS devices.
The information that's stored on a smartphone can help address crucial questions in an investigation, revealing whom an individual has been in contact with, where they have been, and what they've been doing with the device. As new features are added to the device and more apps are made available through the App Store, the amount of information that's stored on iOS devices is continuously growing.
Mobile forensics can be defined as the process of recovering digital evidence from a mobile device under forensically sound conditions using validated means.
The kind of evidence we can recover from a device depends on the device itself and what techniques are used for data extraction, but generally, smartphones contain personal information such as call history, messages, emails, photos, videos, memos, passwords, location data, and sensor data. No other computing device is as personal as a mobile phone.
Typically, the examination process should reveal all digital evidence, including artifacts that may have been hidden, obscured, or deleted. Evidence is gained by applying established scientifically based methods and should describe the content and state of the data fully, including where it is located, the potential significance, and how different data sources relate to each other. The forensic process begins by extracting a copy of the evidence from the mobile device. Once a copy is available, the next step involves analyzing the data, identifying evidence, and developing the contents of a final report.
The new golden age for iOS forensics
Over the past 3 years, the digital forensics industry has undergone a major revolution.
In 2019, the discovery of the checkm8 exploit for iOS devices was a complete game-changer as it opened new doors for digital forensics investigators, allowing full filesystem extractions of hundreds of millions of Apple devices. If you've never seen a full filesystem extraction before, you'll probably be surprised by the extent and variety of data that the device stores!
Checkm8 is based on an un-patchable hardware flaw that lives directly on the chips of iOS devices, ranging from devices running Apple's A11 chip down to the A5 generation. This includes devices from the iPhone 4S to iPhone X and several iPads.
This vulnerability is specifically a BootROM exploit, which means it takes advantage of a security flaw in the initial code that iOS devices load during the boot process, and it can't be overwritten or patched by Apple through a software update.
At the end of 2019, checkra1n was released, the first public, closed source jailbreak based on the checkm8 exploit. Digital investigators and forensics analysts have quickly adopted checkra1n to get access to the device's filesystem and keychain; however, as with all jailbreaks, this solution has several drawbacks as using a jailbreak inevitably modifies some data on the device's filesystem and is not considered forensically sound.
For these reasons, vendors such as Cellebrite, Elcomsoft, and Oxygen Forensic have developed proprietary solutions based on the original checkm8 exploit that work by patching the device's RAM. These tools allow investigators to perform full filesystem extractions without touching system and user partitions and without making any changes to the device as the exploit runs in memory.
In other words, on selected devices, the checkm8 vulnerability can be exploited to extract the full filesystem without actually jailbreaking the device. The following table shows the list of devices that are vulnerable to the checkm8 exploit:
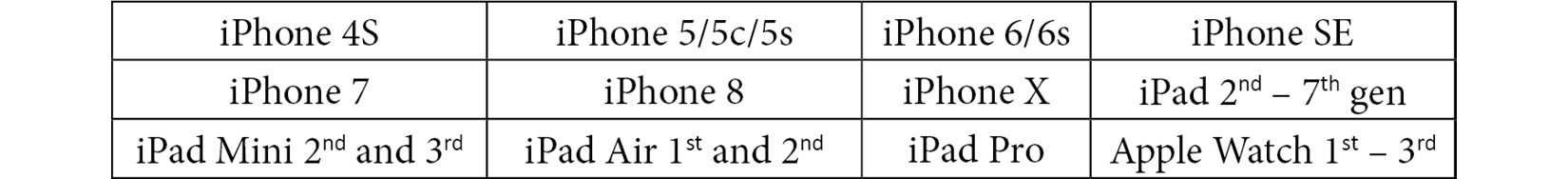
Table 1.1 – Devices that are vulnerable to the checkm8 exploit
To exploit checkm8 for a filesystem extraction, your device must be compatible, and it must be running a supported iOS version. This is a major drawback as newer devices, such as the latest iPhone 13, are not supported. There are, however, other options.
In 2020, vendors such as Elcomsoft and Belkasoft introduced agent-based extraction, a new acquisition method that allows full filesystem extractions without jailbreaking the device. Once installed on the device, the agent escapes the sandbox through software exploits, gaining unrestricted access to the device and establishing a connection between the device and the computer. Agent-based extraction is forensically safe, and it is usually a lot faster and safer than most jailbreaks. At the time of writing, supported devices include all iPhones from the 5s up to the iPhone 12, running iOS versions 9.0 to 14.3.
In May 2020, a major update for the unc0ver jailbreak was released, adding support for devices based on A12-A13 chips. At the time of writing, unc0ver supports jailbreaking all devices from the iPhone 5s up to the iPhone 12. Supported iOS versions range from iOS 11 to iOS 14.3.
Although jailbreaking a device allows full filesystem extraction, it's not considered a forensically sound process. An investigator should consider safer options such as checkm8 or agent-based extractions first if they're supported.
Tip
It's important to note the difference between checkm8-based extractions and jailbreaking the device through checkra1n or unc0ver. Tools such as Cellebrite UFED and Elcomsoft iOS Forensics Toolkit leverage the checkm8 exploit to temporarily provide access to the entire filesystem by running the exploit in the device's RAM. When the extraction is complete, the device will reboot as normal. No permanent changes will be made to the device.
On the other hand, jailbreaking the device will leave permanent traces and will also require installing third-party packages such as Cydia or AFC2, making additional changes to the device.
Challenges in iOS forensics
Smartphones are considered live, dynamic systems, and for this reason, they pose several challenges from a forensic perspective because data and files are constantly changing.
One of the main complications that a digital investigator may face is dealing with a locked device: recent iOS updates make passcode cracking almost impossible and other options will have to be considered to extract as much data as possible.
The growing number of devices and the variety of the software they run makes it extremely difficult to develop a single tool and a consistent workflow to address all eventualities. This is usually because a particular method that's used to extract data from one device will stop working when a new version of iOS is released; in fact, forensic extraction tools usually rely on security vulnerabilities to gain access to the device's filesystem and extract a lot more data than what you would normally find in an iTunes backup, or even to unlock a device when the passcode is unknown. When a new iOS update is released, these vulnerabilities could potentially be patched, thus rendering the tools useless.
The modern investigator will have to take these issues into account when approaching an Apple device and decide, on a case-by-case basis, what the best technique will be to obtain the broadest amount of valuable evidence.