Application of detection levels
Incident response and SOC teams will usually be concerned with having low false positive rates. Remember that these are the alarms that are triggered even though nothing malicious actually occurred. Having a false positive rate that is low will help ensure that any alarms that fire and are brought to the SOC analyst's attention are a true concern. The reason for this is that evaluating and investigating a false positive can cause a massive drain on the incident response or SOC resources. Investigating an alarm that is not malicious in nature and actually a benign activity does not provide any improvement to network defenses. The trade-off for focusing on a low false positive rate is that there will be a higher level of false negatives due to the higher requirements for alerts to trigger. This, in turn, means that there will be a higher percentage of activity that is malicious in nature but will not trigger any alarms.
A threat hunter is concerned with the inverse of SOC requirements. When setting the bar for what is considered anomalous and requiring further investigation, the threat hunting team accepts having a high false positive rate. High false positives will help ensure that the respective false negatives are kept very low. A threat hunting team can accept a high false positive rate due to the scope of their hunt being very narrow compared to the scope an SOC would be monitoring on a day-to-day basis.
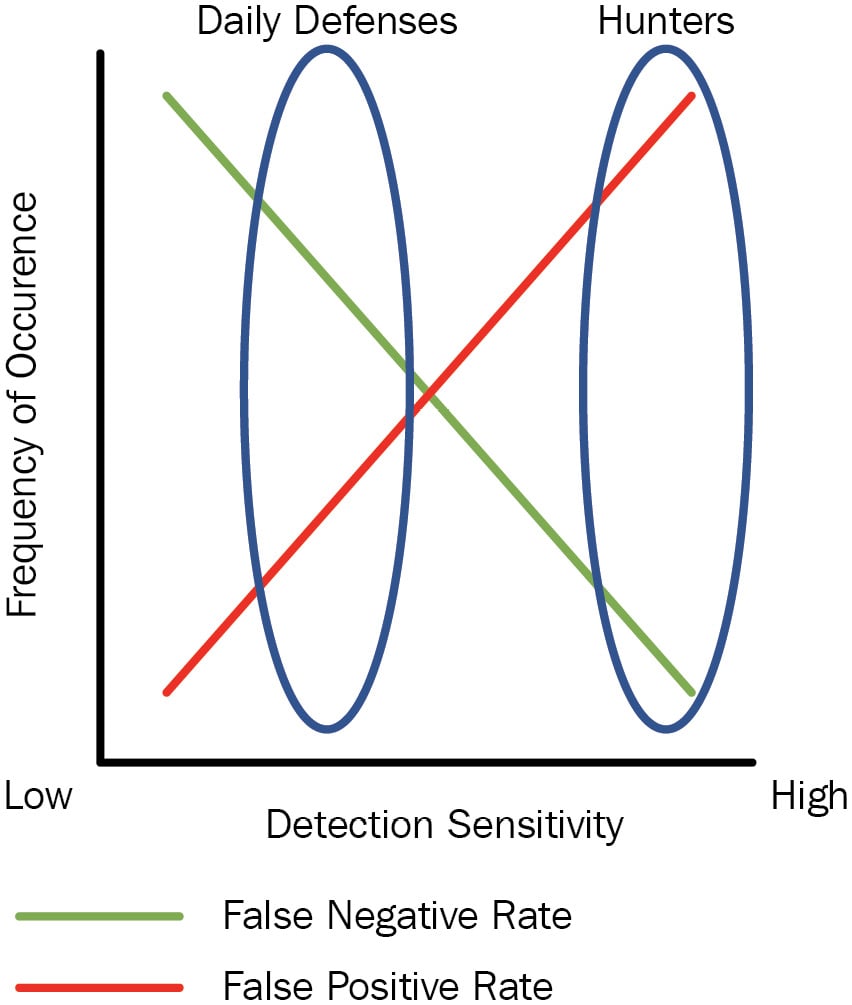
Figure 1.3 – Daily defenses versus hunt team heuristic sensitivity threshold
The preceding diagram depicts this consideration of false negative versus false positive. For a business just getting into threat hunting, this could mean a paradigm shift for parts of their team in how they measure success on a daily basis. An example would be an organization that uses the false positive rate as a measurement of success. For daily defenses, this will normally be tuned so that it is low, thus enabling the front-line cyber defenders to focus only on the things that truly matter and not waste time with dead ends. When the organization starts hunting and needs to measure their success, the false positive rate for a hunt team should be very high. Leadership looking at those statistics might be trained to think that this is a bad thing when, in fact, it is expected.