Classification of major cybercrimes
While the digital dimension may (on different levels) improve people’s lives, it leaves them vulnerable to emerging threats, potentially with severe implications. The internet has acted as a new pathway for criminals to conduct their activities and launch attacks with relative obscurity. Cybercrime, also known as computer crime, refers to activities carried out by means of electronic devices, computers, or the internet to conduct illegal acts (European Commission, 2021). The majority of cybercrime is conducted by hackers or cybercriminals who are after financial gain. However, there are times when cybercrime tries to harm systems or networks for factors other than economic profit. The following list classifies three major categories of cybercrime:
- Crimes against people: This type of cybercrime aims to exploit human weaknesses, such as greed and naivety. It includes cyberstalking and harassment, extortion, defamation, credit card fraud, identity theft, human trafficking, distribution of child pornography, and so on (Panda Security, 2021).
- Crimes against properties: Some online crimes take place against properties, such as a computer or a server. This category of cybercrime includes cyber vandalism, virus transmission, cybersquatting, copyright infringement, cyber trespass, distributed denial-of-service (DDoS) attacks, and so on (Swier Law Firm, 2021).
- Crimes against governments: This kind of cybercrime may significantly impact a nation’s sovereignty. Cybercrimes against a government include accessing confidential information, cyberwarfare, industrial espionage, network intrusions, cyberterrorism, and so on (Arora, 2016).
These days, cybercrime is running rampant. Warren Buffet, the billionaire mogul and philanthropist, believes that cybercrime is the number one issue with mankind and that cyberattacks are a much bigger threat to humanity than nuclear weapons. Mass attacks in cyberspace may even constitute a threat to international peace and security. Cybersecurity Ventures has estimated that the global cybercrime damage costs in 2025 will reach 10.5 trillion US dollars. The following figure shows the global cybercrime damage costs in 2021 (Morgan, 2020):
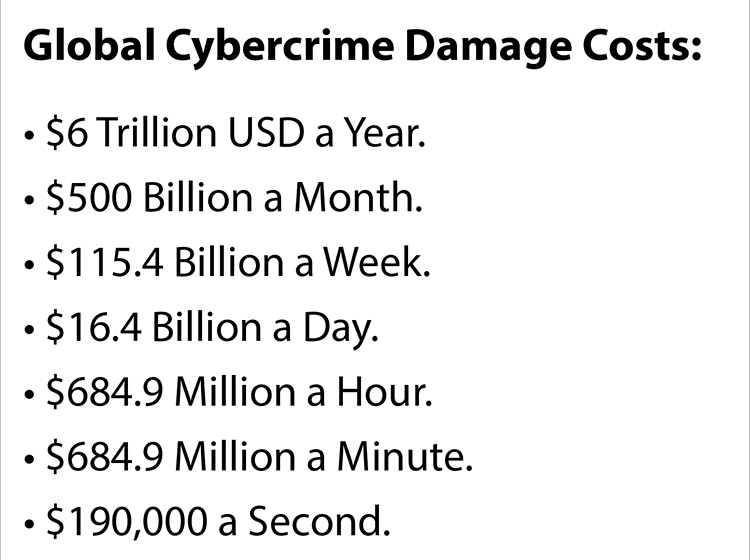
Figure 1.1 – Global cybercrime damage costs in 2021
With the pandemic (COVID-19) worsening and a fatigued remote workforce, the potential attack surface for cybercriminals has expanded dramatically. Cyber-related crimes continue to rise in scale and sophistication, and every day, essential services, businesses, and individuals become victims of malicious/harmful cyberattacks. Even though cyberattacks are not tangible as physical attacks are, they can be as impactful and devastating (Lallie et al., 2021). Some critical cybersecurity statistics and trends are set out here:
- The worldwide cybersecurity market is projected to reach 170.4 billion dollars in 2022 (Contu et al., 2018)
- Data breaches exposed 36 billion records in the first half of 2020 (Goddijn, 2020)
- 94 percent of malicious malware is delivered via email (Phishing Box, 2019)
- The average cost of a single data breach was 3.86 million US dollars in 2020 (IBM Security, 2020)
- Human error is to blame for 95 percent of cybersecurity breaches (Hourihan, 2020)
- In 2020, the average time to identify and contain a breach was 280 days (IBM Security, 2020)
As can be seen, taking cybersecurity seriously is of vital importance. Nowadays, data has become the most valuable asset in the world, and applying proper cybersecurity techniques may protect individuals and organizations from severe damage. You might be asking how to fight cybercrime given its ubiquity. Here are some wise recommendations for preventing cybercrime on your computer and your personal data:
- Keep your operating system and software updated: By maintaining an updated operating system and software, you can use the most recent security fixes to safeguard your machine.
- Use antivirus software: It’s wise to use antivirus software to defend your PC from threats. You can scan, identify, and get rid of hazards with antivirus software before they become a problem. You may rest easy knowing that this protection is helping to safeguard your computer and your data against cybercrime. Maintain antivirus updates to get the best level of security.
- Use strong passwords: Use secure passwords that are impossible for anyone to guess, and don’t save them elsewhere. Or, to make this simpler, use a trustworthy password manager to generate strong passwords at random.
- Never open attachments in spam emails: By clicking on links in spam emails, other unsolicited messages, or unknown websites, consumers can also become victims of cybercrime. To maintain your online safety, avoid doing this.
It is predicted that fast-paced changes in technology will cause a dramatic increase in cyberattacks. The following section describes the various types of cyberattacks, as well as how cybercrime has evolved throughout the years.
Types of cyberattacks
Digitalization is no longer part of a 1930s science-fiction movie. It is the past, present, and future of humankind. Digital transformation has positively changed almost every aspect of people’s lives, but at the same time, it has brought with it many downsides. Cyberattacks have moved beyond harming computers, networks, and smartphones. Cybercriminals can attack literally anything with a heartbeat or an electronic pulse—for example, people, cars, refrigerators, railways, coffee machines, planes, baby monitors, power grids, drones, nuclear facilities, and so on.
A cyberattack refers to an action where a threat actor (attacker)—or a group of threat actors—attacks a computerized information system to steal, manipulate, alter, or destroy confidential data (Pratt, 2021). Because of the internet’s global existence, hackers can be physically positioned anywhere in the world and still cause harm. While an attacker can use various techniques to penetrate a system, most cyberattacks rely on similar methods. Here is a list of the most common types of cyberattacks:
- Phishing attack: Phishing is a popular type of cyberattack where hackers send deceptive messages to unsuspected users. These messages appear to come from reputable sources—that is, friends, family, colleagues, banks, internet service providers (ISPs), and so on. Most phishing messages are delivered via email, and their goal is to do the following (Phishing.org, 2021):
- Steal sensitive data such as credit/debit card numbers and login credentials.
- Install malware on the victim’s machine. The information obtained by the hackers can be used to steal the victim’s identity, request money, or seek thrill/pleasure.
- Malware attack: Malware is a general term used to describe malicious software. This type of software is maliciously installed on a user’s system (without their consent) and can perform various harmful tasks (McAfee, 2021). Spyware, ransomware, viruses, and worms are all types of malware attacks. Some forms of malware, such as ransomware, are designed to extort the victim in some way. This is done by purposefully encrypting their files and then demanding a fee to be paid to get the decryption key (Ovide, 2020).
- DoS attack: This type of attack works by using compromised devices to flood the targeted system with requests in order to disrupt its normal functioning. A DoS attack aims to make the system inaccessible to its intended users—that is, employees, clients, account holders, and others. Services affected may include emails, websites, and online banking. Also, attackers have the ability to use multiple compromised devices and cause even more harm. This is known as a DDoS attack (Weisman, 2020).
- Structured Query Language (SQL) injection attack: An SQL injection is considered the number one threat to web applications. It occurs when an attacker interferes with the queries an application (website) makes to its backend/server-side database. The hacker injects malicious code into the server and forces the server to display the user’s database contents—for example, usernames, passwords, secret questions, and other information. An SQL injection is usually used to bypass authentication, disclose confidential information, or alter data (Ping-Chen, 2011).
Cyberattacks have a number of detrimental repercussions. When an attack is conducted, it may result in data breaches, which may cause data loss or manipulation. Companies suffer financial losses, a decrease in customer trust, and reputational harm. We employ cybersecurity to prevent cyberattacks. Networks, computers, and their component protection from unwanted digital access are known as cybersecurity.
Evolution of cybercrime
Cybercrime’s evolution is easy to trace and coincides with the evolution of the internet itself. The internet provides a rich environment for criminal activity, ranging from vandalism to human trafficking to intellectual property theft.
The early years
Cybercrime first appeared in telecommunications and specifically with phone phreaking, which topped in the 1970s. Phone phreaking is a slang term coined to describe people who exploit hardware and frequency vulnerabilities of telephone signaling in order to make free calls (Madsen, 2019). Exploring telecommunication systems was not (and is not) illegal in and of itself, but exploiting this technique to get reduced phone rates is illegal. As landline communications became more secure, phone phreaking became much less common (Brush, 2021).
The time computer security turned real was around 8:30 p.m. on November 2, 1988. That night, a malicious virus, called Morris Worm, was propagating at a remarkable speed on the internet (Federal Bureau of Investigation (FBI), 2018). It was one of the first worms distributed via cyberspace and received mainstream attention. This kind of advanced software quickly transformed itself into the first large-scale DDoS attack. Systems around the globe were overwhelmed, and around 10 percent of the world’s computers malfunctioned (Seltzer, 2013). Apart from privately owned computers, the worm took down computer servers in government facilities, hospitals, military bases, and so on. The actual damages were difficult to quantify, but it is estimated that the episode resulted in multi-million-dollar losses (Capitol, 2018).
The 1990s to 2000s
Although there was cybercrime at the beginning of the internet’s creation, the first big surge of cybercrime came with phishing emails in the 1990s. Phishing is a type of social engineering attack (the practice of deceiving people to obtain valuable information). Phishing has made it easy to send numerous scams and/or viruses to people’s email inboxes. Phishing emails often imitate a trusted source, such as a phone provider (National Cyber Security Center UK, 2019). They often include official-looking graphics, email addresses, and dummy websites to trick the user. Hackers send these kinds of emails to steal passwords and bank account numbers or to infect systems with viruses (Alkhalil et al., 2021).
Post-2000s
At the beginning of the 21st century, cybercrime was no longer controlled by criminals who were hacking computer systems just for fun or notoriety. The growth of the digital economy had changed the criminal landscape dramatically. Criminal gangs introduced a professional element into the world of cybercrime. Cybercrime had become so popular that well-organized networks of criminals started collaborating to pull off massive heists over the internet (Heussner, 2011). The following are some forms of cybercrime that appeared at the beginning of the millennium and still exist today:
- Cyber extortion: This type of cybercrime occurs when hackers steal and hold electronic files of an individual or a business until a demanded ransom is paid. Cyber extortion includes actions such as ransomware, email ransom campaigns, and DDoS attacks (McMillan, 2017).
- Attacks against critical infrastructures: Commonly attacked critical infrastructures include the energy, water supply, and health sectors. Transportation, public sector services, and telecommunications are also vulnerable. Such attacks draw the attention of several law enforcement authorities and pose an exaggerated risk (Allianz, 2021).
- Cyberterrorism: The potential damage cyberterrorism can cause provokes considerable alarm. Numerous cybersecurity experts, private companies, and politicians have publicized the possibility of criminals hacking into governmental and private computer systems. Cyberterrorism has the potential to cause severe damage to any country’s military, financial, and service sectors (Weimann, 2004).
- Online human trafficking: This kind of cybercrime is a serious and growing problem. Digital technology and the internet are fueling worldwide growth in human trafficking. The internet provides traffickers with enormous potential to seek out and groom marginalized individuals. Sexual perpetrators can scan the internet to find vulnerable individuals of all ages (Allen, 2019).
- Exploitation of children: There is also a very real and nasty side to cybercrime. Almost every day, criminal gangs are being caught with child pornography. Never before has it been so easy for pedophiles to come into contact with children. This kind of material can be found all over the internet, including the notorious Dark Web (Broadhurst and Ball, 2021).
Cybercrimes are a global threat and are more rampant than ever in the year 2022. With the COVID-19 pandemic worsening and a fatigued workforce, the potential attack surface for cybercriminals has increased in size dramatically. Cybercriminals and the sophisticated technologies they use are often based abroad, making international cooperation between agencies essential. Apart from disrupting the current generation of cybercriminals, it’s of vital importance to prevent young individuals from slipping into cybercrime. Regional organized crime units, as well as international law enforcement—for example, the FBI, Interpol, and Europol—must encourage young people with cyber skills to use their knowledge wisely and avoid any cyber-related illegal activities.
The internet’s three primary levels
The internet is an immense archive that contains vast amounts of data. Web data extraction, also known as web scraping or web harvesting, is one of the most advanced tools for gathering information from around the internet. Such tools can help companies with the following:
- Gaining market and competitive intelligence
- Keeping up to date with changes to compliance and regulation terms
- Staying abreast with developments in their industry
This level of data extraction provides access to a large repository of content that is usually hidden (Cerami, 2017). The following screenshot shows the internet’s primary levels (How big is the Internet, 2018):
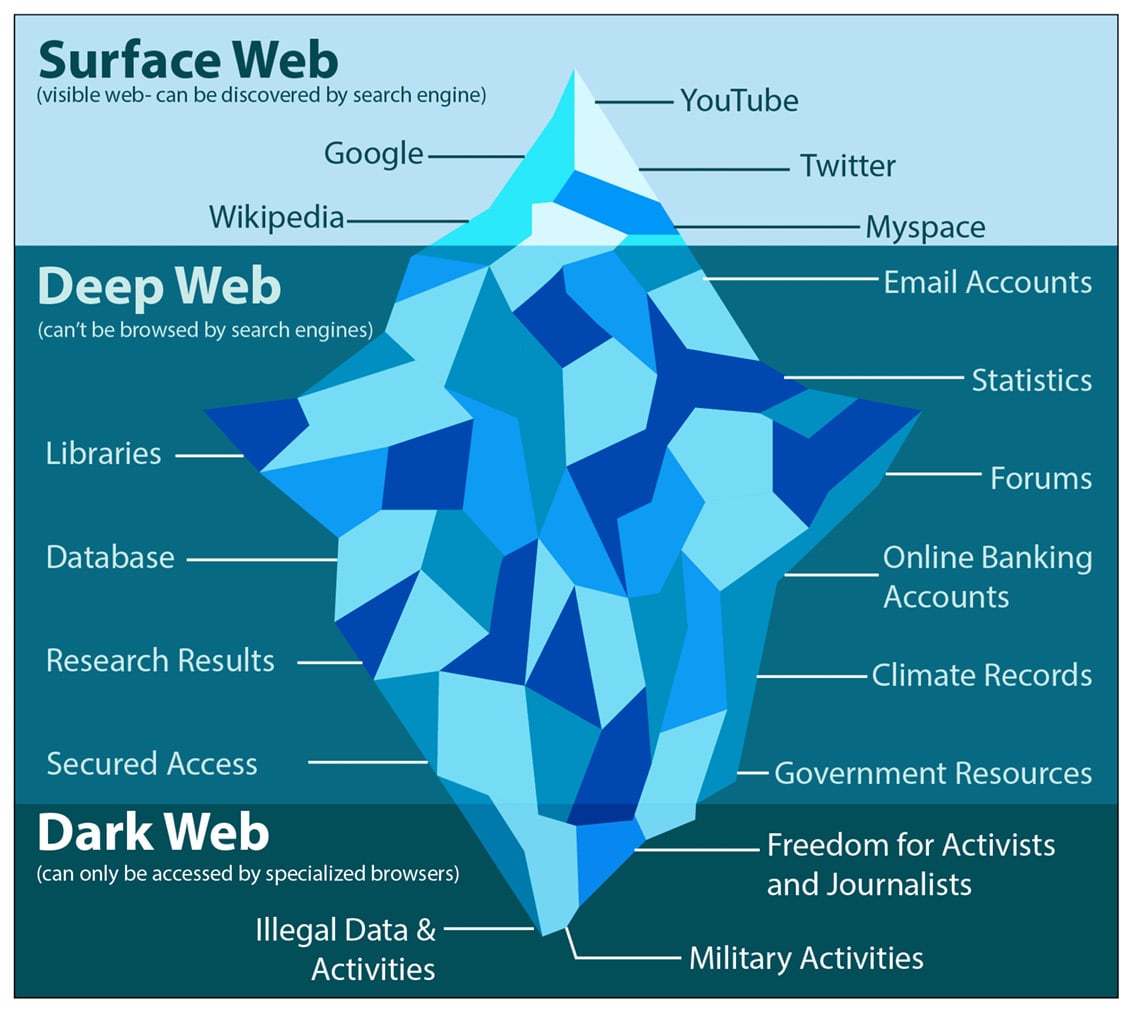
Figure 1.2 – The three primary levels of the internet
The internet consists of three levels: the Surface Web, the Deep Web, and the Dark Web. Each one of them is unique and is being used for specific things:
- The Surface Web: The Surface Web, also known as the Indexed Web, Visible Web, or Lightnet, is anything you can find on the regular World Wide Web. It is readily available to the general public and the primary entry point for most people. This portion of the internet consists of websites indexed by regular search engines—that is, Google, Bing, Yahoo, and so on. It has only around 5 percent of what is available on the internet. The Surface Web can be accessed using standard web browsers that do not require special configuration—for example, Mozilla Firefox, Microsoft Edge, Google Chrome, Opera, Brave, and so on (Center for Internet Security, 2021).
- The Deep Web: The Deep Web is below the Surface Web and accounts for approximately 90 percent of all internet traffic. It contains most of the internet’s data, and standard search engines do not index its contents. In fact, the Deep Web is so large that it is impossible to precisely estimate how many pages or websites it has. Specifically, it includes websites that require authentication to access them—that is, usernames and passwords. Most of the Deep Web’s contents are related to academic journals, private databases, and medical records. The Deep Web also includes the portion of the internet known as the Dark Web (Kaspersky, 2021).
- The Dark Web: The Dark Web includes sites that cannot be found by conventional search engines and can only be accessed via specialized browsers. When compared to the Surface Web, the Dark Web is significantly smaller, and it is considered a part of the Deep Web. Using the screenshot shown earlier, the Dark Web is at the bottom tip of the submerged iceberg. To navigate this portion of the internet, you need special programs such as the TOR browser. This program will connect you to an overlay network that will mask your IP address, making your online activity highly anonymous. The Dark Web can be used for legitimate purposes as well as to conduct criminal activities related to fraud, weapons, drugs, child pornography, assassinations, human trafficking, zoophilia, and so on (Guccione, 2021).
To sum up, the following are some significant variations between the Dark Web, the Deep Web, and the Surface Web:

Figure 1.3 – Surface Web versus Deep Web versus Dark Web
In conclusion, you must realize that the Dark Web is not a place you decide to visit one morning. Understanding that the majority of ISPs hunt for users of TOR-like services—the most typical entrance point—requires some thought. Use one of the many tutorials available to you if you really want to access the Dark Web to learn how to set it up and where to begin.

























































